Passwords, 2FA and security keys
Passwords to secure one’s own accounts probably want to be kept well, however, above all.
Introduction

The recommendation that you should have a different password for every account has been around for a long time. And meanwhile there are more websites and services that offer a so called 2FA authentication.
But passwords have become a kind of competition between us and the bad guys out there.
I reported about it 7 years ago and the situation hasn’t gotten any better..
Passwordmanager
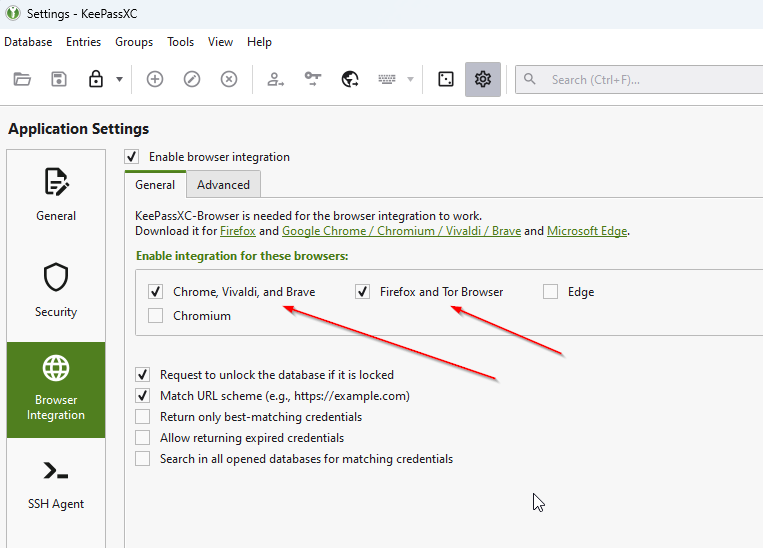
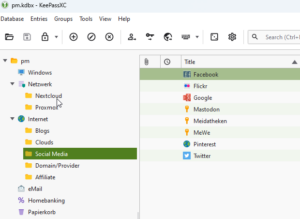 Since you can hardly keep really complex passwords from 15-20 accounts, you use a password manager. In the meantime I switched to KeePassXC. Not because KeePass that I used until then was bad, but KeePassXC offers the better browser integration via a plugin.
Since you can hardly keep really complex passwords from 15-20 accounts, you use a password manager. In the meantime I switched to KeePassXC. Not because KeePass that I used until then was bad, but KeePassXC offers the better browser integration via a plugin.
KeePassXC is available natively for Windows, Linux and MacOS and for Android and iOS there are several apps that can read the database format in any case.
In addition, KeePassXC can handle SSH keys very well, so that you can save yourself some work or inconvenience.
2 Factor Authentication
The 2FA is supposed to offer another piece of security and is now offered by many services. In addition to the password, which you know, a time-based key is generated by a thing that you own (usually a cell phone).
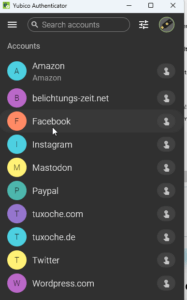
For this purpose, a QR code is generated at the beginning of the login procedure, which can be photographed with an appropriate app, and then the keys can be generated there, which are usually only valid for 30 seconds.
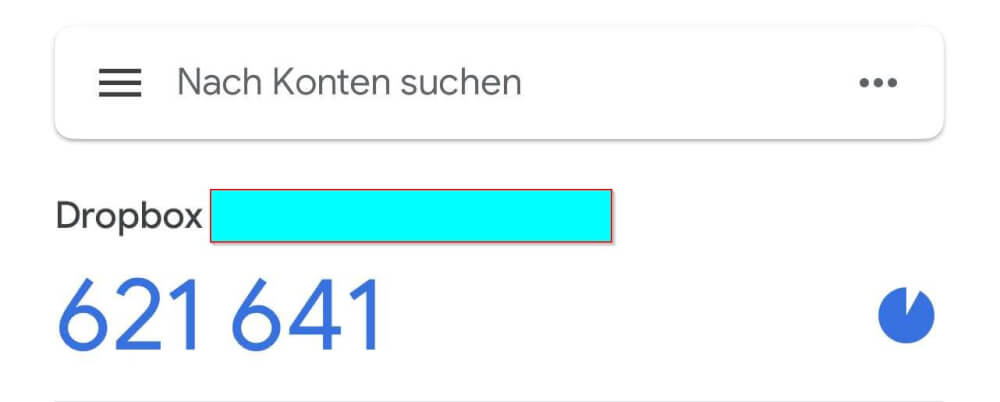
I have used Google Authenticator for years, but as I said, there are several apps. However, such an app should only be able to be opened by entering a password, PIN or similar.
You should write down the start codes and keep them safe. The same applies to backup codes.
Yubikey
The security keys, which are available from Yubikey, are a kind of enhancement of the 2FA method. The keys are in the form of a USB stick, so that USB-A or USB-C can be connected to the PC.
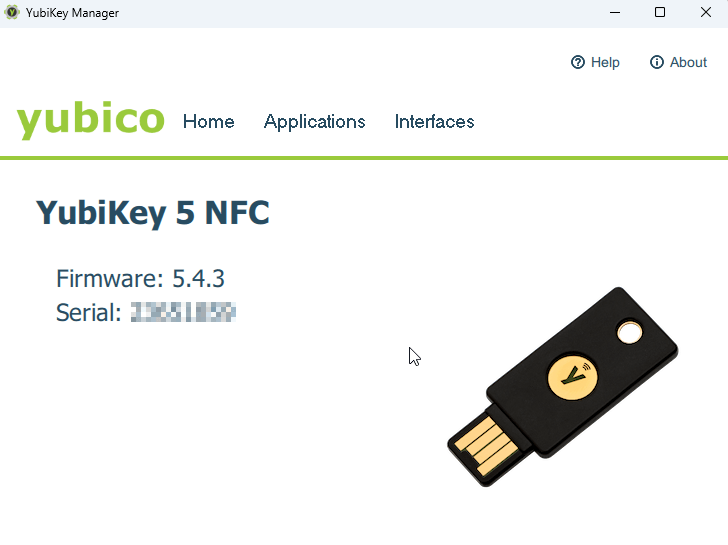
The associated app, however, generates the TOTP code only when the key is further unlocked by tapping the flashing field, so to speak.
 This turns 2FA into multi-factor authentication, so to speak, and should therefore be secure. Here you can use not only the TOTP codes but also Fido2 and other protocols. Depending on the provider, a login can also be changed so that no password has to be entered at all, but only the Yubikey and perhaps a PIN.
This turns 2FA into multi-factor authentication, so to speak, and should therefore be secure. Here you can use not only the TOTP codes but also Fido2 and other protocols. Depending on the provider, a login can also be changed so that no password has to be entered at all, but only the Yubikey and perhaps a PIN.
Conclusion
In any case, you should use a password manager and, where possible, at least set up 2FA so that, in addition to the password, there is another factor that you cannot access via the Internet. Of course a Yubikey or other hardware tokens are the non plus ultra but with a price of arround 50,– € the’r not cheap. And for the case you break or loose one you’ll need two of these keys. But this is up to you to decide.
ciao tuxoche